LanScopeCat
Features Description
Asset Management
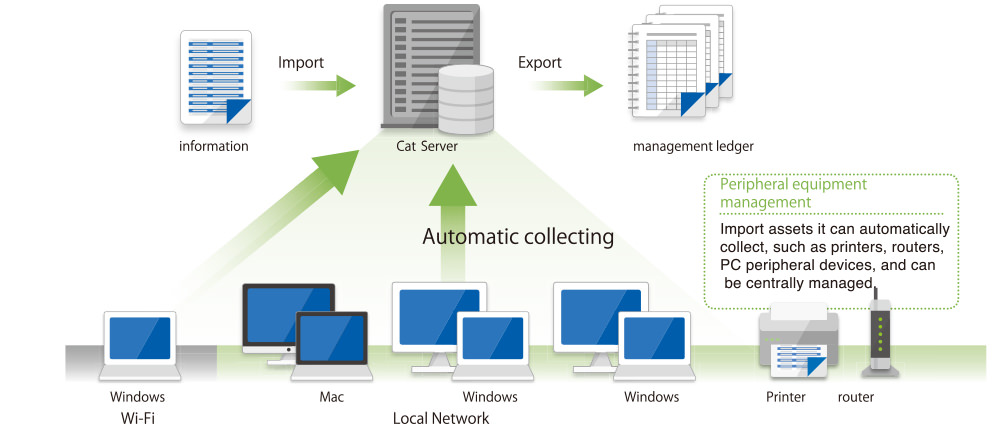
Update hardware and software information every day to maintain an accurate environment and avoid the hassle of managing tasks.
Automatically collect IT asset information and always view accurate information. In addition, keep a history of changes and notify the administrator via email. You can import existing logs or export logs from each generation.
Hardware Assets
Information
Automatically collect more than 50 types of hardware information, such as computer name and IP address, and optional registry data. Can choose to record and manage printers and other peripheral devices.
Software management
Check application updates, messages and questionnaires, and whether application updates are installed on the PC. Categorize allowed and prohibited apps and manage information.
Information Survey
Send a questionnaire from the administrator to the user. Conduct surveys through free responses and drop-down menus to collect information that cannot be collected automatically.
Equipment Management
Manage printers, routers, and computer peripherals in the same area.
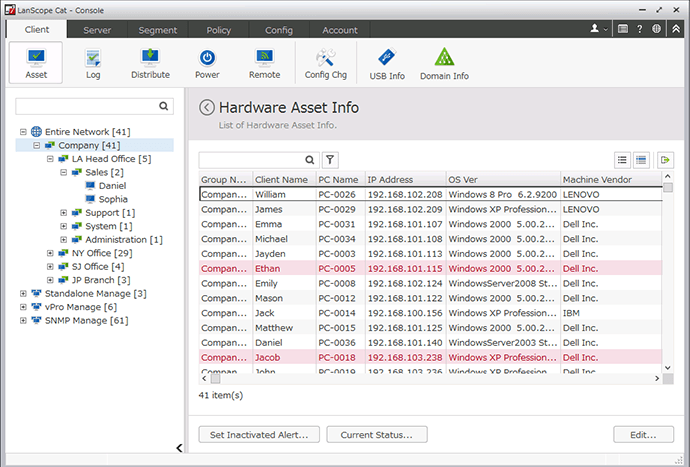
Hardware Assets
Information automatically collects more than 50 types of hardware information, such as computer name and IP address, and optional registry data. Can choose to record and manage printers and other peripheral devices. Moreover, it is possible to check necessary information by searching under various conditions.
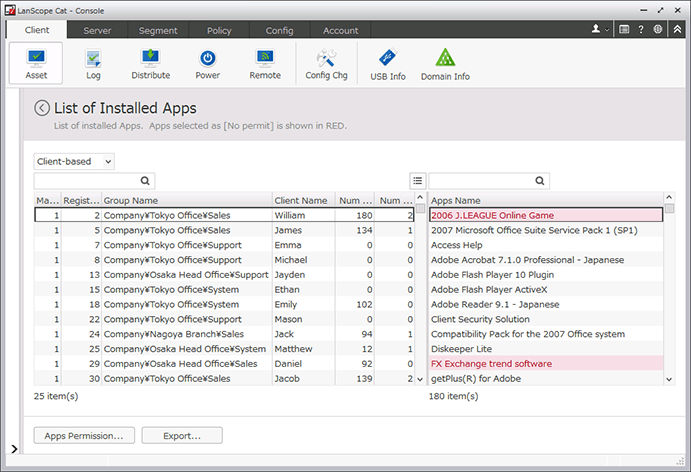
Software Management
Check application updates, messages and questionnaires, and whether application updates are installed on the PC. Categorize allowed and prohibited apps and manage information. For example, the number of machines installed in each application and their product keys.
I can now manage 800 computers in 70 locations on my desk.
I want to replace some old monitors, but I do n’t know the year of purchase of each monitor ... Before using Cat, I had to visit more than 70 offices and check my phone and email archives, but now, I can organize according to the selected type, and it will be sorted out in the ledger without any gaps. This definitely makes my job easier.
Operation log management
By managing PC operation logs, you can improve security and find problems in an emergency, without reducing operational efficiency.
Record PC usage information, such as running applications, printing, document operations, screen view (window title). If there is any operation violation, a warning is displayed to the user, thereby improving safety and morality.
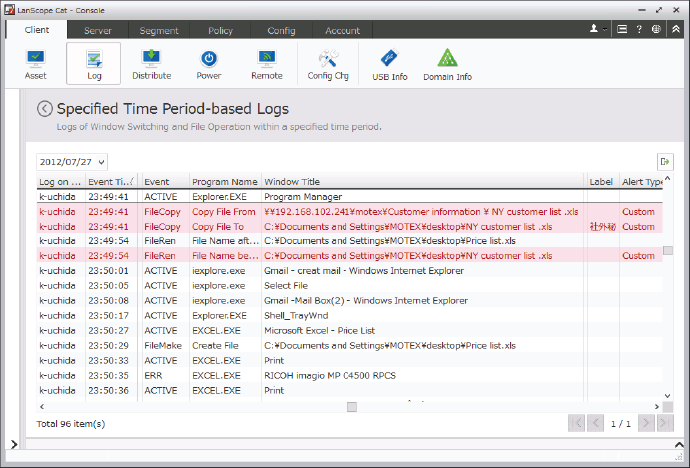
Operation log
Management
Record "who" did "what" and "when" on "which PC". If certain operation violations (possibly information leakage) occur, such as writing the customer list to USB, a warning will be displayed to the user and illegal operations will be prevented.
Operational analysis
View the status of the PC with color-coded graphics.
Print log
Management
Record "who" printed "what" "how many pages" "when" in "which computer". You can find wasteful printing and reduce costs. If a specific document is printed, a warning is displayed to the user and illegal printing is prevented.
Application status management
Record "who" used "those applications" "when" in "those computers". See how many instances and how long each application is running on the PC. Reduce wasted licensing costs by allocating the ideal number of licenses.
Block apps
It is forbidden to start applications that are not related to work or illegal applications. If a specific application is launched, a warning is displayed to the user, and the application (such as a game or an application that may cause information disclosure) is suppressed.
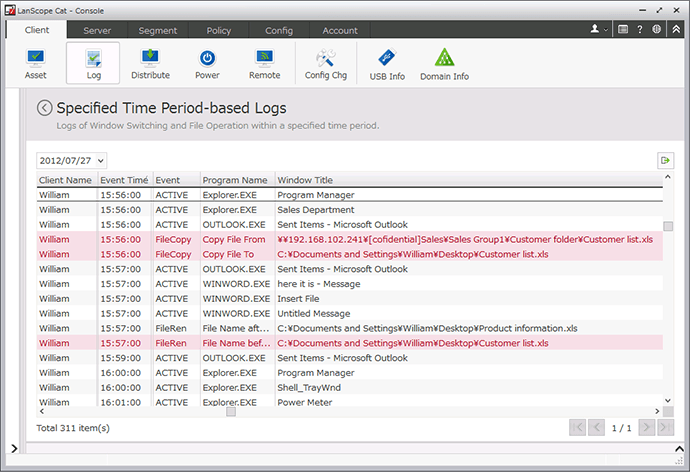
Operation log management
Record "who" did "what" and "when" on "which PC". If certain operation violations (possibly information leakage) occur, such as writing the customer list to USB, a warning will be displayed to the user and illegal operations will be prevented.
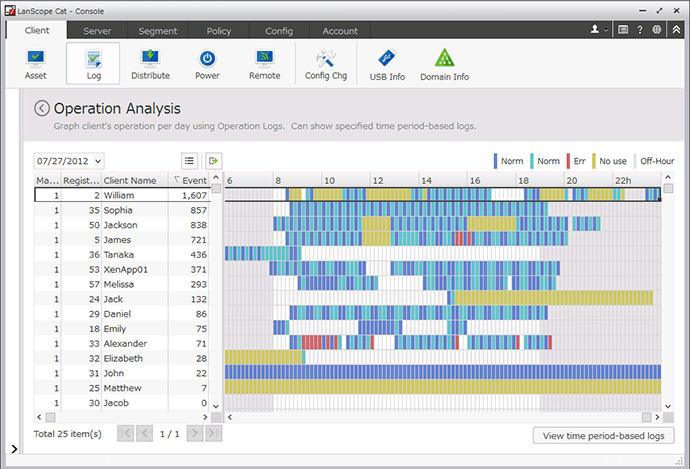
Operational analysis
View the status of the PC with color-coded graphics.
Operation log management provides me with a healthier work-life balance by improving efficiency.
It allows me to better understand my work so that I can identify and solve problems such as managing applications. In five months, although I reduced the average monthly working hours by 10%, I was able to complete more work.
Browse website management
Monitor website usage and restrict access to illegal websites.
You can save records of browsing websites and control access to specific websites or related categories of websites. Promote users to use appropriate websites and avoid browsing harmful websites.
Browse website management / control
Record "who" browses "which website" "when" on "which computer". If you view illegal websites, you can display alerts or block access. In addition, upload and download can be restricted, and the information posted on the browsing website in IE can be recorded.
White List
The specified keywords are only allowed to access specific websites. Create an environment where you can only access the websites you need for work (such as group software and cloud services).
View and browse web content
By clicking on the URL in the website browsing log and directly viewing the website, you can determine whether the content of the web page is necessary for work.
Analyze web content
View reports that can be sorted by day, hour, or personal computer, and view trends on website viewing data. In addition, in each report, look at the percentage of sites that contain alert keywords.
Website browsing
Management / Control
Record "Who" saw "Which websites" and "When" on "Those computers". If you view illegal websites, you can display an alert or prevent browsing access.
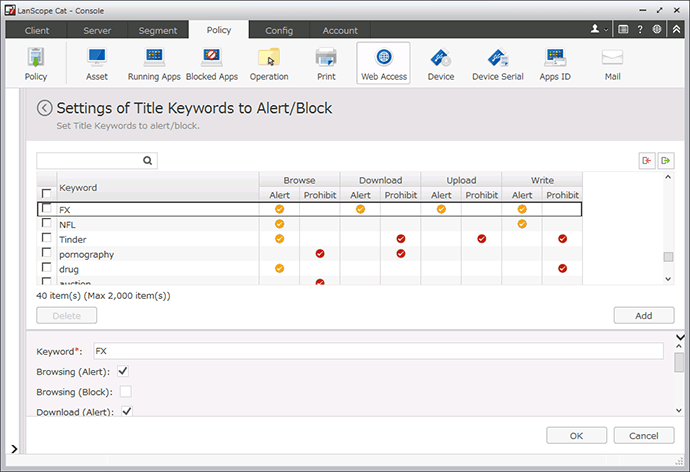
Website browsing control
The specified keywords are only allowed to access specific websites. At the same time, you can limit upload and download, and record the information posted on the Web in Internet Explorer
Website browsing access management can identify suspicious website browsing visits at night and help prevent information leakage.
After we started using Cat, we were able to detect two suspicious network accesses within seven years. With this knowledge, we can prevent the leakage of sensitive information.
Equipment control
Control the use of devices such as USB and CD, and prevent the leakage of important secret information.
Manage all company equipment and restrict its use. If a prohibited device is connected, the user will be notified that the device is prohibited and illegal use is controlled. In addition, by setting the detailed conditions of the PC and the device to suit the workplace, the device is allowed to be used in limited circumstances.
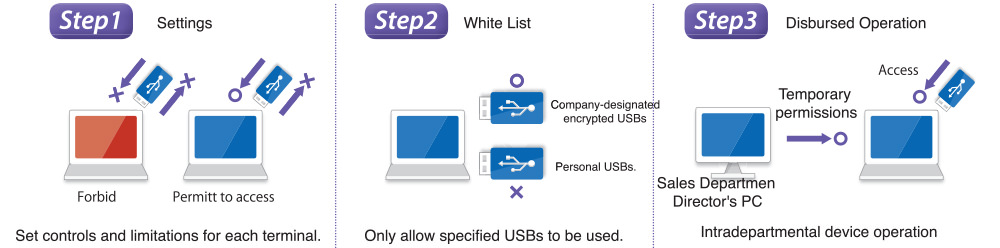
Set usage limits for each terminal device
Control or prohibit the use of CD, DVD, USB, etc. by type. In addition, flexible settings allow each PC to be set to prohibit reading and writing, disable writing only, and so on.
Set USB permissions
Specify the device name (nickname), manufacturer number (serial number) or only the device issued by the company and prohibit the use and connection of other devices.
USB connection information
Display a list of USBs connected to the hosting PC, and see which ones are allowed and which ones are not allowed. You can also enter and edit information required for management, such as user or asset number.
USB manager tool
Managers can allow, deny, or temporarily allow USB management from the PC they manage.
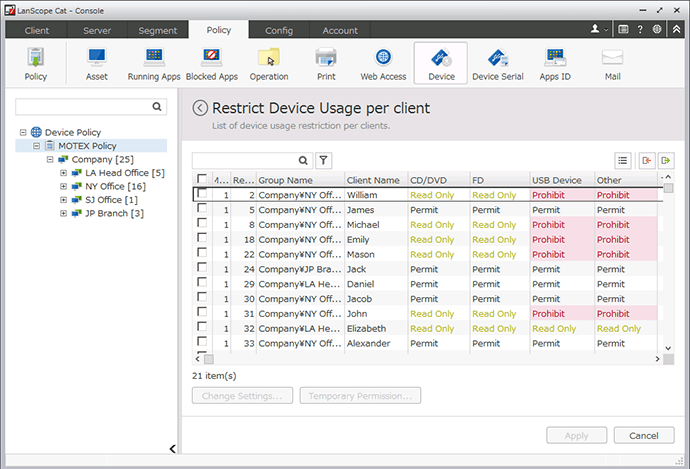
Set usage restrictions for each terminal
Control or prohibit the use of CD, DVD, USB, etc. by type. In addition, flexible settings allow each PC to be set to prohibit reading and writing, disable writing only, and so on.
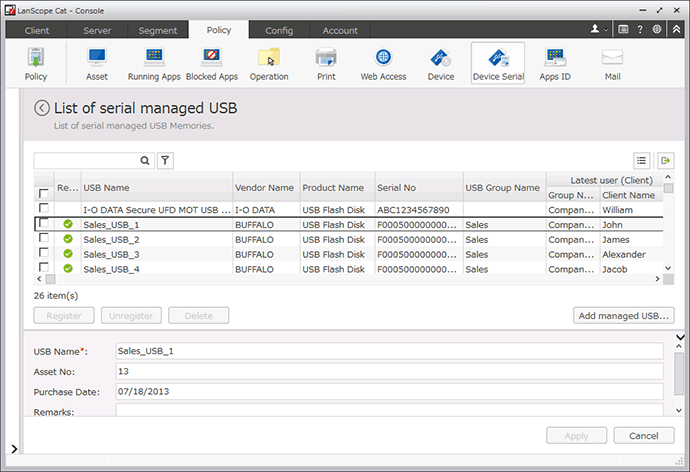
Set USB permissions
Specify the device name (nickname), manufacturer number (serial number) or only the device issued by the company and prohibit the use and connection of other devices.
No more losses or theft! And no longer use personal USB.
Because we process a lot of sensitive information, I often lose sleep because of the thought that this information falls into the wrong hands. However, thanks to Cat, we can now protect our computer and USB and prevent loss or theft. Employees can only use pre-registered USB.
“CAT can track which people and what records and information are on which device through, so the implementation improves the safety awareness of all employees.”
System environment※Based on 100 users
| Server |
|
|---|---|
| Client |
|
- ※ The above system environment is just a suggestion. It will vary depending on the number of users and the size of the collected logs.
- ※ Please build a specific server for LanScope, do not use the same server as the management server of other applications.
- ※ For the database, please use additional products, no additional purchases are required.
- ※ For the web console, Silverlight 5 or higher must be installed.
- ※ LanScope Cat Manager supports ESX and Hyper-V server virtualization.
- ※ LanScope Cat MR agent supports desktop virtualization of XenDesktop,XenApp,Hrizon View,VPCC.