LanScopeCat
What is LanScope
80%Leaking happened Internal
Main reason for leak message is through email,video,photocopy to provide data.
Because of leaking company will get damaged
Those cost will happened for investigation to victims , also damaged trust and brand of company , effect of once leak message is inestimable , 80% of time is coming from Internal.
Stop
information
Leaking
Happen
Where is weakeast point?
PC is the most damaged property,
It's reasonable Because PC is
majoy connect between staff and web.
Usually upload,email,copy to any kind of move data storage , Data base and file server is most value property should be protect all the time , you also need to be careful about Payment card , it had chance been copy by Suspect. As right to own property , we think staff abuse it , we usually get proof some staff using non certified equipment to get value data from company.
There has lots of way to protect servers for External threat , how ever the policy for client is simple , this is reason to leak meassage , but the really threat is come from internal , In fact U.S. been successfully to deal with external threat many years , still have problem to deal with leak message from internal.
Recommended control
The reason of data theft and ilegal behavir is staff been corrupted . although to stop all of them is impossable , but some way could be low chance happened or dect it faster .
-
Beware of data breaches
The most of leaking , we see behavir to help tranfer data to external network , this is good spot to place dection products.
-
Publish audit results
From the perspective of awareness, the results of anonymous access audits are regularly published.
LanScope Cat is a comprehensive software package that contains necessary functions for information leakage countermeasures and IT asset management. LanScope Cat is able to select only the necessary functions, is a security tool that can solve the IT asset management and information security problems faced by many businesses, and supports business success.

Use our Cat System(Check,Action,Trace), We build the system you need to manage your important assets,
Implement information security measures and stop leaks.
-
 Check
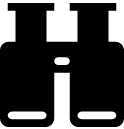
CheckWe understand the types of computers on your network and how they are used.
-
 Action
Action通By implementing appropriate measures against risks, major problems can be prevented.
-
 Track
TrackIn the worst case, we review past data and track down the cause of the problem.
 |
|
|---|---|
| Property |
We automatically collect information to determine the usage of IT assets (including PCs and software) and create an environment to achieve the best performance by setting appropriate resources in the appropriate places. |
| Log |
By recording computer usage, we can suppress illegal and non-commercial use. In addition, we also understand and analyze the usage and working status of IT assets to improve operational efficiency and productivity. 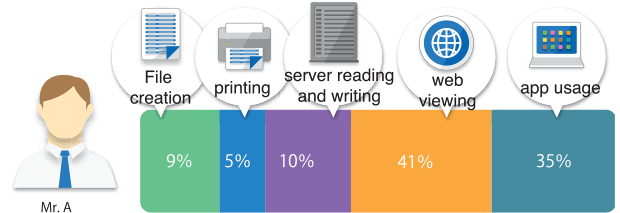
|
| Safety |
By visualizing data usage and controlling the paths through which information may be leaked (Web, device, application, PC), we protect personal information and company secret information. 
|